VPN
This feature is currently available in Alpha version
Single Tenant/Exclusive instance required.
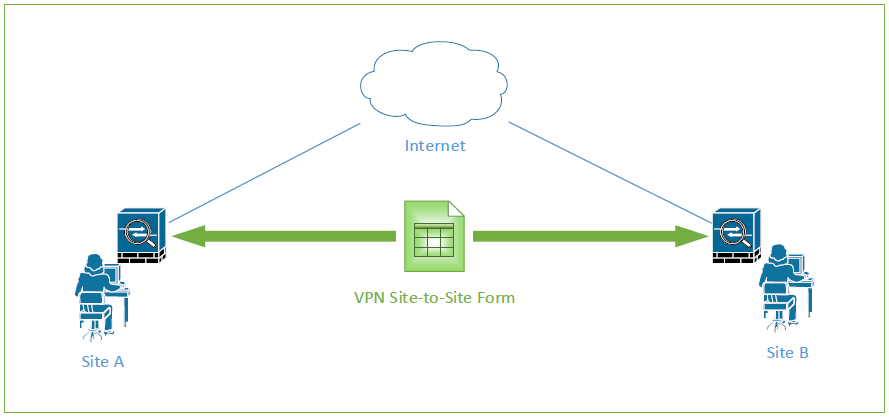
Our Site-to-site VPN allows you to safely connect multiple LAN networks (a local-area network that spans a relatively small area) in different locations using a Cloud VPN tunnel (Google Cloud managed service, see documentation). Firstly, the feature protects the logins to the Bloomreach Engagement Application, preventing unauthorized access to single tenant instances. Compared with remote access VPN, the site-to-site VPN eliminates the need for each device in a network to run its own VPN client software, is easier to scale and the latency of the network is much lower. Secondly, the VPN tunnel can be used as an additional security layer for data imports and API calls from campaigns.
Site-to-site VPN works in the following way: The Cloud VPN connects the relevant LAN networks to the GCP Virtual Private Cloud (VPC) network through an IPsec VPN connection. Traffic traveling between the two networks is encrypted by one VPN gateway and then decrypted by another VPN gateway. This protects the data as it travels over the internet.
IPsec or Internet protocol security is a protocol suite that encrypts the entire IP traffic before the packets are transferred from the source to the destination. It is capable and responsible for authenticating the identities of the two nodes before the actual communication takes place between them.
Site-to-site VPN from Bloomreach Engagement
Securely connect local-area network (LAN) in order to allow a secured tunnel between Bloomreach Engagement, the client's on-premise data warehouse, and Bloomreach Engagement users' workstations.
There are three possible VPN connections, that will be analyzed throughout this article
- When logging into Bloomreach Engagement´s single tenant instance, a client may use VPN enabled workstation to log in.
- Bloomreach Engagement may import and export from data sources on the client's internal network through a secured VPN.
- While working, Bloomreach Engagement VPN may call API endpoints on the client's internal network.
Bloomreach Engagement login
The feature protects the logins to the Bloomreach Engagement Application by preventing unauthorized access. The site-to-site VPN eliminates the need for each device in a network to run its own VPN client software, makes it much easier to scale, and the latency of the network much lower.
There are three possible set-ups for securing Bloomreach Engagement login:
| Set-ups | Description |
|---|---|
| Public access | Application is accessible on the public domain from the public internet. Users can access the Bloomreach Engagement application from any public network. This setup is used on all Bloomreach Engagement multi tenant instances. |
| Public access with IP whitelist | Application is accessible in the public domain from a limited set of IP addresses. These IP addresses are whitelisted using Cloud Armor. Users can access it from a whitelisted office network. Optionally, Bloomreach Engagement consultants can have this access when connected to Bloomreach Engagement VPN. |
| Intranet VPN access | Application is accessible on the intranet domain (computer network for sharing information) only from the intranet network. Users can access the Bloomreach Engagement application only by using VPN-enabled workstations on an internal network. This configuration does not support access for Bloomreach Engagement consultants. A client must provide a Custom SSL certificate for the application intranet domain. |
Practical integrations and limitations
Site-to-site VPN allows Bloomreach Engagement to import and export from/to client internal file storage/databases and invokes HTTPS endpoints on the client's internal network.
With VPN enabled, our customer support team would not be able to access your application. If you need support, agents will operate with screenshots provided by you. We'll do our best to help you via guiding and suggesting the possible root causes of the issues you might have.
In case the problem persists, we can try to arrange a session where you can share your screen. However, scheduling a session may take a longer time, depending on the capacity of our Customer support, and this option should be used in cases when we believe it would help to solve the problem faster.
Webhooks
Scenarios can send requests to external API endpoints and to internal endpoints when VPN is configured. Read more about webhooks.
Requirements for webhooks to an internal API endpoint
- Enable Static IPs.
- Must use a secured HTTPS endpoint.
- SSL (Secure Socket Layer) certificate must be issued by one of the publicly trusted certificates authorities.
- The domain name is resolved from either: a public Domain Name System (DNS) or a static domain-IP mapping (/etc/hosts file provided during VPN setup).
- You can also configure the internal firewall to allow requests from a list of Static IPs.
Unsupported
This part outlines the limitations of VPN when integrating for Webhooks
- IPv4 and IPv6 endpoints (=network endpoint) without a domain name (for example,
https://34.76.115.106/api.php) would be unsupported - Unencrypted HTTP endpoints (for example,
http://my.example.com/api.php) - SSL certificates signed by custom certificate authorities
Imports through VPN
| Name | Function | Limitations |
|---|---|---|
| Imports from SFTP | With a Bloomreach Engagement VPN, users can import files from SFTP on a public domain. | SFTP imports don't support Static IPs and can't connect to the intranet SFTP server |
| Imports from PostgreSQL and MySQL | PostgreSQL and MySQL imports can use Static IPs and can connect to intranet servers. | |
| Imports from MS SQL | Imports from this Microsoft storage will be secured by the Bloomreach Engagement VPN | MS SQL imports don't support Static IPs and can't connect to the intranet MS SQL server |
Tracking and data API
Bloomreach Engagement APIs (public tracking API, private Customers API, private Catalogs API) are available on the public domain from the internet.
Unsupported
- IP allow list for private customers' API
- VPN intranet with sole access to the private customers' API
Networking
Bloomreach Engagement is using Google Cloud VPN (IPsec compatible), which can be configured as Classic VPN or HA VPN (with a 99.99% service availability).
Google Cloud VPN can connect to multiple gateways, which allows it to connect multiple networks on the client side (office network, data warehouse network, ESB network).
Bloomreach Engagement ingress (data entering Bloomreach Engagement)
There is a separate internal load balancer used when the Intranet VPN Bloomreach Engagement login is enabled. This load balancer requires a custom certificate and internal domain name to be provided by the client.
Bloomreach Engagement egress (data entering Bloomreach Engagement)
All requests from the Bloomreach Engagement platform (imports, exports, webhooks, monitoring ping) originate from a proxy with Static IP addresses. We recommend creating allow rules on the client's firewalls.
Unsupported
Cloud VPN with multiple gateways can't be set up when IP ranges on client networks collide with each other
Monitoring
Bloomreach Engagement can be configured to monitor VPN tunnel uptime. An ICMP probe regularly checks network availability on the client's network if the client provides a server that responds to ping requests. Monitoring probe requests originate from internal Static IP addresses.
Availability
VPN setup is available for single-tenant and Exclusive instances. We support setting up 1 Cloud VPN for each Bloomreach Engagement instance.
Updated 7 days ago
